Over the last decade or so, the Internet has been expanding at an alarming rate. Industries like Ecommerce and ESports have quadrupled in size in a relatively short time, and in a few years, they might even rival major industries like oil.
With this fresh influx of money into the Internet, it has never been more dangerous to remain unprotected online. Regular cyberattacks like phishing, spoofing have become more brazen threatening small and large corporations alike.
Pharming attack is one of the latest and most dangerous cyberattacks on the Internet. It is targeted at small-scale businesses and regular Internet users alike. It is a more advanced version of phishing, and without proper education, it can cause regular people to lose their identities and savings.

What is Pharming Attack?
Like what phishing does, a pharming attack is generally an Internet attack but it is a higher form than regular phishing (a social engineering attack that steals the personal information of victims without quite alarming them). Pharming attacks lure unsuspecting victims to malicious websites generated specifically for stealing users’ information. Once they enter their information, the hackers steal from the victim’s account, blackmail them for money, or sell their information to the highest bidder.
What makes the pharming attack aroused? In order to carry out a pharming attack, the pharming attacker/cybercriminal can either get a malicious program installed on the user’s computer system or the user deliberately logs onto a DNS (Domain Name System) server that’s been infected by the attacker.
Pharming attacks are far higher than normal phishing attacks, which means they are expected to be difficult to prevent as well. They are much more difficult to see through, and they require some level of expertise and security to avoid. Unlike what regular phishing attacks do, pharming targets the users as well as computers. It redirects the computer by changing the IP address and redirecting traffic to a malicious website.
Pharming attacks imitate regular websites and fool victims regardless of whether they follow the link in the email or not. As far as the correct URL is followed, the victims will be led to the pharming website that is designed to trick them into giving up their details.
What Leads to the Name of “Pharming”?
Pharming is the combination of “phishing” and “farming”. Based on the originality of the name, it’s easy to know pharming is correlated with phishing while it is more serious than phishing. Phishing seduces Internet users to click a malicious link while pharmers are able to “plant” malicious codes on Internet users’ devices.
It’s necessary to understand how different are pharming and phishing since that helps you easily understand the significance of cybersecurity.
Pharming vs. Phishing
Generally speaking, pharming is usually mixed up with phishing. Then, what is the exact difference between pharming and phishing?
Simply put, the difference between phishing and pharming is that phishing is done through a specific link sent by a cybercriminal to internet users. In this case, the user will choose and decide to click and follow that link. On the other hand, the pharming attack is not done through a link. It is done by directing the traffic on an original and unique site to a fake site by changing the host’s file on a victim’s computer or by infecting the DNS server of the original site.
How does Pharming Attack Work?
Pharming attacks can happen in one or two ways. It can either take place through a process known as poisoning or it can be carried out with the help of an application.
The poisoning pharming method is used when hackers exploit the vulnerabilities of a DNS server software by altering the rules, and connecting users to spoofed websites. DNS servers are computers that connect browsers to their respective IP addresses. They help users access websites they want to access. When this is altered or messed with, it is possible to reroute an unsuspecting user to a different site entirely without their knowledge. When DNS servers have been successfully tampered with, the servers are referred to as “poisoned”.
The second and most popular method is through malware. Instead of going through all the trouble of hijacking a DNS server, pharmers simply alter the contents of the host files of the computer. Host files are files that contain a list of previously visited sites and their IP addresses. When a Pharmer alters the host files, he links certain website names to the IP addresses of his spoofed websites. This way when the user inputs the URL, it will request a different IP address instead of the correct and safe one. The malicious application used in pharming can mostly be found on illegal websites. Once this application downloads and installs, it will begin to corrupt and change files. This method of pharming is used to gather numerous victims. It is far more effective than DNS cache poisoning, in that, the attack cannot be dealt with at once.
How Should I Know When I’m Suffering from Pharming Attack?
Pharming isn’t a ghost that leaves no trace behind. Two signs can tell you that you’re suffering from a pharming attack and they are quite useful for us to prevent pharming attacks.
Sign#1. If an insecure connection is met on your browser, it’ll be possible you’re suffering from a pharming attack.
Do you notice the difference between “HTTP” and “HTTPS” as browsing on the Internet? Their difference, “s”, refers to “secure”. Therefore, “HTTP” connection is insecure while “HTTPS” is secure. Normally, as you type a website into the blank on a browser, the “HTTPS” will be seen at the beginning, indicating a secure connection. So if your website begins with “HTTP”, it indicates that you’re suffering from a pharming attack.
However, current browsers feature security functions in themselves. For example, as you type a website on Google Chrome, it directly comes into a secure mode.
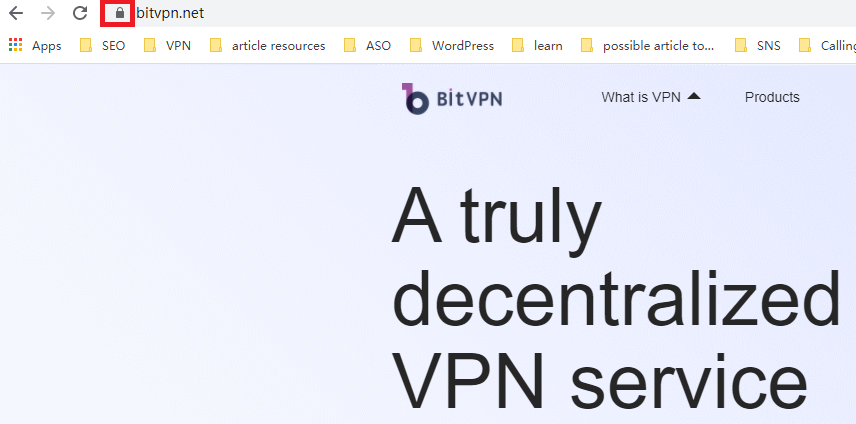
The “lock” icon at the beginning of the website indicates the security of the browsing. If a website you’re visiting is insecure, the browser will tell you immediately. In this sense, a secure browser is able to help you filter some malicious websites.
Sign#2. If any abnormality is met on websites, it’ll be possible that you may suffer from a pharming attack.
People should be sensitive to any change taking place on their Internet. If a website you’re using features spelling errors, unfamiliar fonts, or color, or it just looks unusual or illegitimate without any reason, it’ll mostly be a fraudulent website created by pharmers to lead you to fill in personal information on it.
How to Prevent Pharming Attack?
Although it is incredibly difficult to identify a pharming attack until it’s too late, there are proven ways to avoid pharming attacks altogether.
Using trustworthy internet service providers to cut the source that may lead to pharming attack
Most established internet service providers are large and well established enough to repel most pharming attacks directed towards their customers. They have up-to-date security and redirect users who have been led astray as soon as a pharming attack is noticed.
Use a VPN to establish an encrypted tunnel to protect against pharming attacks
A VPN can be used to protect Internet users’ online security and privacy. It stops any third party or ISP from tracking your online trace based on your IP address. A VPN also establishes an encrypted tunnel through which all your communications between your device and the Internet are well hidden from others.
Check the URL for errors to prevent pharmers seducing you to click it
The biggest weakness of pharming attacks is when pharmers fail to completely create a perfect replica of the websites they targeted. This means that there will be distinct differences between the pharmer’s websites and the original websites. The first and most common indication is a misspelled brand name or poor site construction or programming.
Use HTTPS when browsing to easily stay away from pharmers
Most financial websites are encrypted and offer an extra layer of security. This extra layer of security is denoted by the HTTPS. HTTP websites do not have security because they are not encrypted and as a result, and it’s dangerous to visit them. Therefore, internet users should not disclose sensitive information on websites with no HTTPS protection.

Avoiding illegal websites to keep away from any pharming misinformation
Illegal websites offer their subscribers and users access to valuable information and products for free. Most times, these free information and services are embedded with a dangerous malicious application. Sometimes it might be malware that destroys files, and other times, it could be pharming malware.
Use antiviruses software
There is numerous well-reviewed antivirus software available on the market. Most of them can detect and remove dangerous pharming malware and protect users as they browse the internet. Picking an effective antivirus that guards against most pharming attacks should be fairly easy for most users.
You May Also Like:
- How to Tell if Someone is Spying on My Phone and How to Stop That
- Ask Your Employees These Questions to Easily Test Their Cybersecurity Awareness
- What’s Computer Hacking and How to Prevent It
- What is Ransomware? Everything You Should Know About Top 1 Possible Cyberattack in 2021
- Affected by Facebook Leak? How to Stay More Private on Social Media
